A flaw in the security of the Election Commission of India website was putting the personal information of potentially every voter in India at risk, revealing sensitive information such as names, phone numbers, and email addresses. Using such information, scammers could have attempted to phish for access to bank accounts and stolen money, or impersonated people to cause other kinds of harms.
And although the electoral roll is public data, the site also makes it very easy to get peoples’ street addresses, which could also open up other kinds of misuse.
This flaw was first spotted earlier this week by security researcher Karan Saini, who works as a software developer with Bengaluru based IT firm, HasGeek. Saini reported the matter to CERT-In, the Indian Computer Emergency Response Team, which is the nodal agency dealing with cybersecurity issues in the country, but has not received a response on the matter.
For the latest news and more, follow HuffPost India on Twitter, Facebook, and subscribe to our newsletter.
“Identifiers such as phone numbers and email addresses attached to this kind of data can not only be useful for cyber criminals attempting to target individuals, but also by political parties for delivery of targeted messaging and election campaigning,” Saini said.
This was elaborated on by former BJP worker Shivam Shankar Singh, who talked about how the BJP’s election machine made use of a wide variety of personal data to target voters, as was detailed in an investigation by HuffPost India.
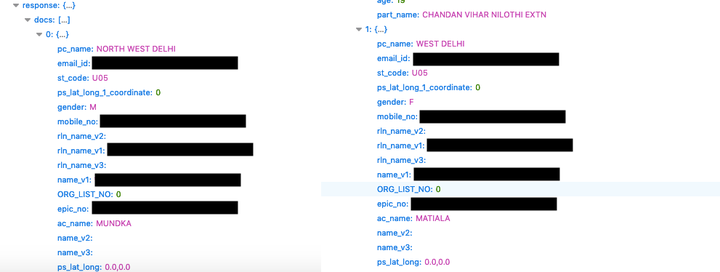
Explaining the flaw to HuffPost India, Saini said, “Essentially, the Electoral Search website is programmed to return all the data whenever queried (including phone/ email when available) but to only display some of this information on the browser.”
This means that when using the Electoral Search website to look up information, a user would see the Voter ID number, name, age, father or husband’s name, district, polling station, and assembly and parliamentary constituencies — but the website itself was sending a lot of additional information.
What’s worse, this was being sent without any safeguards, and Saini demonstrated the method to reveal the information, which does not take any programming skills or specialised knowledge, just needing a few clicks on the website itself. While we are not reproducing the steps Saini used, HuffPost India was able to confirm that the process works, and takes less than a minute to carry out.
We have written to the officials seeking comment on this matter, and will update this article on receiving a response.
[Update: Despite still not responding to queries, the issue was fixed after this article was published on HuffPost India.]
“In the website, age is a range, so if you enter 20, you will get results for 19, 21, and 22 too,” Saini said. “Once the captcha for a particular search has been provided, all subsequent pages of information can be retrieved without having to re-enter the captcha, with each page of results showing the details of 15 voters. The full home address and street address is revealed as well, but that is legitimately meant to be public. However, the name, email, and phone number are also exposed.”
One solution is to make it easier for security researchers to bring these issues to the government’s notice, and incentivise the researchers by offering bounties for bringing in bugs and security flaws. Instead, however, people working in the space have repeatedly told HuffPost India that the very opposite often happens, with threats of legal notices being the more common response.
Saini also previously authored a report exploring the issues security researchers and ethical hackers faced when attempting to interact with the Government.
“Reporting security flaws on Indian Government websites and services is often an arduous process,” Saini said. “The lack of an enabling infrastructure surrounding vulnerability reportage often hinders the work of whitehat hackers.”
“Indian Government departments are generally inattentive when it comes to acknowledging and acting on vulnerability reports,” he added. “One does not get to know whether the issue they have reported is going to be mitigated, and even if so, how long it will take, or what priority they are treating it with.”
Ironically, this data leak is happening at around the same time that India has finally started the process of bringing in a data protection bill, which sets serious fines against companies that leak the personal information of people, at Rs 15 crore or 4% of total revenue.
Indian government websites have a history of leaking personal data, such as a government website that tracks medicine sales and revealed the name and phone number of a man buying medicines for erectile dysfunction, or another government website that accidentally revealed the precise latitude and longitude location of Muslim families, Dalit families, Hindu homes and even Zoroastrian families in Andhra Pradesh.
Security on government websites has been a long-running issue in India, and unfortunately, the challenges here aren’t merely technical, but also attitudinal. For example, while speaking to HuffPost India, officials in the Andhra Pradesh government stated that data security in the state isn’t a hacking problem, but an awareness problem. As they explained, citizens data is spread across a vast range of departments, of varying levels of technical awareness, and it’s rarely the core focus of any department, leading to it being relegated to a tick box rather than a serious priority.