
Israeli surveillance firm NSO Group, whose spyware Pegasus was used to surveil journalists and human rights activists in India and around the world, is facing a sudden upsurge in scrutiny thanks to WhatsApp suing the company.
Although companies that make spyware usually remain below the radar, Eva Galperin, Director of Cybersecurity at the Electronic Frontier Foundation (EFF) posted a link to the Product User Guide for Pegasus, which gives a lot of insight into what the software actually does—and how it’s pitched to governments.
We read the Pegasus user guide, and found out how it works, what its unique selling points are, and understood how it was used to surveil journalists, human rights activists, and others in India and around the world.
The guide also shows how the dashboard-driven systems can be misused, and the problems that can be caused by using such a system. Here’s what we found out.
For the latest news and more, follow HuffPost India on Twitter, Facebook, and subscribe to our newsletter.
What does Pegasus promise?
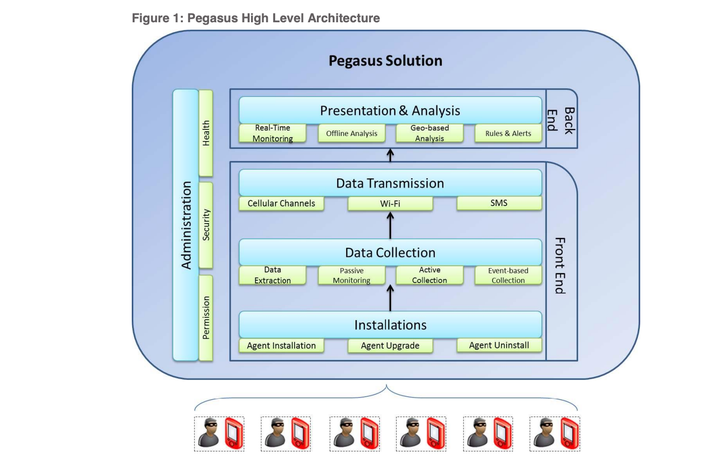
Pegasus is a software designed for governments to use — that much is clear when reading the user manual. The guide highlights why a government would choose this spyware over other options — which is also a reminder that governments around the world have invested heavily (and continue to do so) in the field of surveillance.
In the user guide, Pegasus is described as “a world-leading cyber intelligence solution that enables law enforcement and intelligence agencies to remotely and covertly extract valuable intelligence from virtually any mobile device.”
It notes some of the problems with mobile interception — a growing reliance on encryption, an abundance of communication applications, inaccessible targets (due to face to face meetings, or the use of private networks, for example), virtual identities, SIM replacement, and so on. And comes to the conclusion that rather than trying to solve all these issues one by one, completely taking over a target’s phone is the best way to proceed.
As per the guide, organizations that deploy Pegasus are able to overcome the challenges mentioned above to achieve unmatched mobile intelligence collection:
- Unlimited access to target’s mobile devices: Remotely and covertly collect information about your target’s relationships, location, phone calls, plans and activities – whenever and wherever they are.
- Intercept calls: Transparently monitor voice and VoIP calls in real-time.
- Bridge intelligence gaps: Collect unique and new types of information (e.g., contacts, files, environmental wiretap, passwords, etc.) to deliver the most accurate and complete intelligence.
- Handle encrypted content and devices: Overcome encryption, SSL, proprietary protocols and any hurdle introduced by the complex communications world.
- Application monitoring: Monitor a multitude of applications including Skype, WhatsApp, Viber, Facebook and Blackberry Messenger (BBM).
- Pinpoint targets: Track targets and get accurate positioning information using GPS.
- Service provider independence: No cooperation with local Mobile Network Operators (MNO) is needed.
- Discover virtual identities: Constantly monitor the device without worrying about frequent switching of virtual identities and replacement of SIM cards.
- Avoid unnecessary risks: Eliminate the need for physical proximity to the target or device at any phase .
“The Pegasus solution utilizes cutting-edge technology specially developed by veterans of intelligence and law enforcement agencies. It offers a rich set of advanced features and sophisticated intelligence collection capabilities not available in standard interception solutions.”
So user-friendly, even the government can deploy it
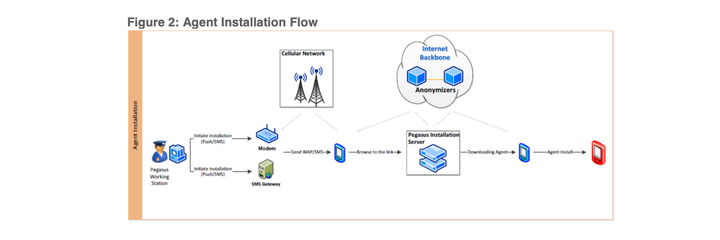
The guide notes that for Pegasus to start collecting data from your target’s smartphone, a software based component (“Agent”) must be remotely and covertly installed on their device. “Injecting and installing an agent on the device is the most sensitive and important phase of intelligence operation conducted on the target device. Each installation has to be carefully planned to ensure it is successful. The Pegasus system supports “various installation methods.”
This can be done through a push notification with a link, which gives no indication on the device that anything is happening, the guide notes. Where this is not possible, the guide recommends social engineering, using a text message or email, and “luring the target to open it. Single click, either planned or unintentional, on the link will result in hidden agent installation.”
Interestingly, the user guide also revealed a limitation of Pegasus. It only works using the system browser, or Chrome on Android, so if you instead use a third-party browser on your phone it could actually prevent Pegasus from infecting your device.
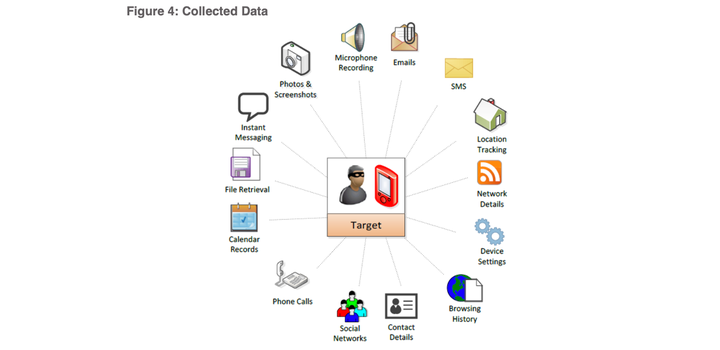
Upon successful agent installation, a wide range of data is monitored and collected from the device:
- Textual: Textual information includes text messages (SMS), Emails, calendar records, call history, instant messaging, contacts list, browsing history and more. Textual information is usually structured and small in size, therefore easier to transmit and analyze.
- Audio: Audio information includes intercepted calls, environmental sounds (microphone recording) and other audio recorded files.
- Visual: Visual information includes camera snapshots, photos retrieval and screen capture.
- Files: Each mobile device contains hundreds of files, some bear invaluable intelligence, such as databases, documents, videos and more.
- Location: On-going monitoring of the device location (Cell-ID and GPS).
According to the user guide, tracking is possible in real-time, with stored history being accessible as well as continuous future monitoring. Data is transmitted as long as the battery is above 5%, and the device is not on a roaming network. On roaming, it only transmits the data via Wi-Fi—crucial data can even be shared via text messages, although it can “occur in his billing report, and thus should be used sparingly.”
Driven by dashboards
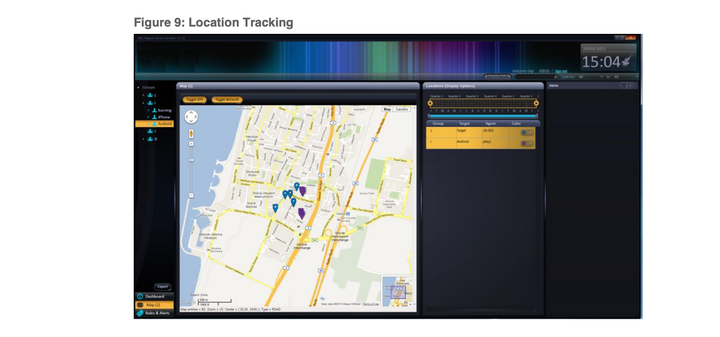
Of course, as is the norm with any software intended for the government, Pegasus also comes with a range of graphs and dashboards for its users. It can carry out geographical analysis, and show multiple targets on a single map; provide an intelligence dashboard with highlights and statistics; and carry out a timeline analysis.
“The collected data is displayed in an easy-to-use intuitive user interface and when applicable emulates popular display of common applications. The intuitive user interface is designed for a day-to-day work.” According to the guide, there’s also a photo viewer, and a screen capture tool, which can show exactly what is on the victim’s screen in real time. Meanwhile, geo-fencing can automatically start recording when a target visits a particular location, or meeting detection could automatically start up a recording session when two targets meet at the same location. Content detection can look for keywords, and automatically record those messages.
In many ways, this fits in perfectly with what we’ve seen from governments around the country. In Andhra Pradesh, an entire state runs on dashboards — which include a giant CCTV network, and dashboards tracking what people are saying about the government on social media. The central government has also been trying to get a Social Media Communications Hub off the ground. This SMCH will be used to track all social media platforms and find people that are not satisfied with the government. And around 40 different agencies are already using a tool called AASMA, which can also track citizens’ social media activities. As is the present norm, the tool provides a single dashboard view of all the information in the system.