In the world of data security, there is an exception to the Law of Conservation of Mass, which says matter can neither be created nor destroyed.
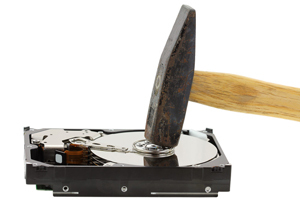
Regarding data—that wealth of digital information, from emails to electronic records, from private missives to government secrets, from company documents to corporate memoranda—there are different degrees of destruction. Those factors range from the perception that data are gone, that a simple press of the DELETE button erases everything, to a combination of physical effort and the application of sophisticated technology to ensure that data are, in fact, no more.
Recent stories about Russian hacking and allegations of foreign interference in the U.S. presidential election are but one example of issues involving data.
Consider, too, the consequences of not protecting (or destroying) data in general. Indeed, the failure to conclusively eradicate data invites breaches that are financially devastating and professionally decimating to executives and enterprises alike.
According to data gathered from breached organizations, the average cost of this event is close to $6 million ($5.9 million), or $201 per record or line item. Data breach incidents involving the loss or theft of data-bearing devices continue to increase, making the cost exceed $18 per record or line item.
Microsoft also reports that the median number of days that attackers stay dormant within a network before detection is well over 200. A study from the Information Systems Audit and Control Association (ISACA) further asserts the following:
"The majority of data breach victims surveyed, 81 percent, report they had neither a system nor a managed security service in place to ensure they could self-detect data breaches, relying instead on notification from an external party. This was the case despite the fact that self-detected breaches take just 14.5 days to contain from their intrusion date, whereas breaches detected by an external party take an average of 154 days to contain."
These statistics underscore the importance of having a military-grade solution for corporations, data centers, governmental agencies and organizations with the strictest data destruction standards.
Take, for instance, secure hard drive shredding: The act itself happens at a client's site, so those in attendance can see the most advanced resources of their kind—including the deployment of shredding trucks to remove all destroyed materials—guarantee that data are no more. This level of shredding, which is otherwise exclusive to the Department of Defense (DOD), is now commercially available.
Gaston Wilder, Executive Vice President of Business Development for Data Destruction, Inc., says:
"Secure data destruction is a critical part of the IT asset disposition and e-waste recycling process. It is essential to destroy data with options such as mail-in-services to onsite hard drive shredding, based on the needs—and the desired level—of data destruction for each entity."
This precision is of particular concern for HIPAA-compliant data destruction, because doctors and insurers—as well as patients and their advocates—cannot risk having this information become the domain of thieves, hackers and all manner of criminals.
Data destruction should be methodical, comprehensive and definitive. To achieve that goal, and to do so with skill and expertise, requires greater awareness of this challenge.
Now is the time for this campaign to begin.