A Palestinian hacker took matters into his own hands late last week when he discovered a Facebook bug and was rebuffed by the company's official engineers.
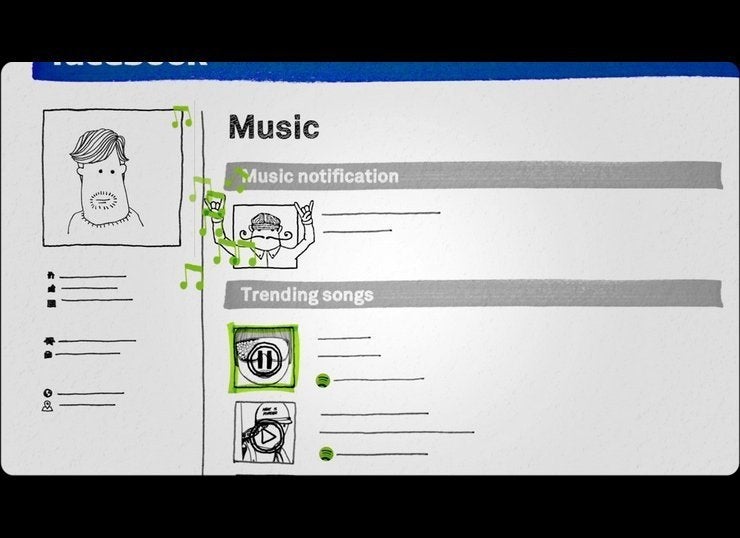
Khalil Shreateh, a computer programmer in the West Bank, discovered a flaw that allowed him to post on anyone's wall on the site, even if that user had strict privacy settings. Shreateh initially submitted his find to Facebook's "white-hat" program, a system that lets benevolent computer hackers tell Facebook about security flaws. Facebook pays a minimum of $500 for each bug, as long as the hacker doesn't disclose the loophole before the company has time to address it.
But when the engineering team didn't seem to think the problem was real, Shreateh decided to prove that the bug he found did indeed exist. So, he simply posted on the private wall of Facebook CEO Mark Zuckerberg.
As he tells it on his blog, Shreateh, who has limited proficiency in English, submitted details of the bug twice. He writes that he was told "I am sorry this is not a bug" by a Facebook engineer after the second notification.
That's when, for better or worse, Shreateh exploited the loophole to post a video on the Timeline of Sarah Goodin, one of Zuckerberg's college friends, and on Zuckerberg's page itself.

Minutes after the post on Zuckerberg's Timeline appeared, Facebook engineer Ola Okelola asked Shreateh to describe the exploit by email. Facebook briefly disabled Shreateh's account as a precaution while the loophole was patched on Thursday. Another member of Facebook's security wrote that the lack of complete information and Shreateh's limited English made responding to the request difficult.
We've reached out to Shreateh for comment. In response to the incident, Facebook pointed to an "official comment" posted on Hacker News, where engineer manager Matt Jones wrote that the company "should have pushed back asking for more details here."
But, Jones wrote, that doesn't mean Shreateh will be getting a reward for exposing the bug. By posting on the accounts of two people he wasn't friends with, Shreateh violated Facebook's rules -- disqualifying him from any bounty for the security flaw. Shreateh should have instead created test accounts to try out his discoveries, Jones wrote.
Only a few tech companies -- like Facebook, Google and PayPal -- employ outside white hats to discover security flaws on their sites. But Facebook attracts some of the best outside programmers by paying the highest rewards, a sign of how seriously the company takes security flaws and the likelihood they could cause people to flee the social network.