LAS VEGAS -– In the sea of mohawks, piercings and tattoos, they stood out like uninvited guests. But the federal agents attending the hacker conference held this past weekend were not there to blend in.
They were on an urgent mission: to try to end the severe shortage of cybersecurity experts working for the federal government.
As cyber attacks continue to increase in both number and scale, the government has launched a massive recruiting effort to hire computer-savvy employees who can help defend the nation in cyberspace.
But the push to build the ranks of cyber experts faces challenges, including long waits for security clearances and a hacker community that has traditionally viewed the government with distrust.
The recruiting effort was on full display this weekend at DefCon, the world's largest hacker conference, where officials from the Department of Defense, the Department of Homeland Security and the National Security Agency mingled with 10,000 of the world's best code crackers and extolled the virtues of government service at a panel called "Meet the Feds."
"There are folks here who know how to circumvent security measures," said Daron Hartvigsen, a special agent in cyber crime investigations and operations for the Air Force who attended the conference. "They are part of the skilled workforce we want to reach out to."
The hiring push comes as threats of cyber attacks and cyber espionage are increasing. More than 24,000 files containing classified information were stolen from the Defense Department this spring by foreign hackers. Last week, the security firm McAfee revealed a widespread cyberspying operation from an unidentified country that focused largely on the United States, including six federal government agencies and 13 defense contractors.
THE NEXT 'MANHATTAN PROJECT'
It is unclear how many cybersecurity experts currently work for the government. But officials say the pool of qualified applicants is far too small to meet the demand.
Officials have said the federal government needs 10,000 to 30,000 cyber experts. But in 2008, there were only about 1,000 people in the nation with the technical skills to defend the country in cyberspace, according to Jim Gosler, founding director of the CIA's Clandestine Information Technology Office. A report published last fall by the Center for Strategic and International Studies found that "well under 200" people were graduating each year with the cybersecurity skills needed to work for the government.
In response, the United States has launched a massive cyber recruiting effort that has been called this generation's "Manhattan Project,” setting up camps and holding cyber competitions for teenagers and offering scholarships, internships and jobs in cybersecurity to young adults.
Such efforts are meant to make up for a long history of failing to encourage computer-savvy children and promote science, engineering, and math.
“Unfortunately we have this stereotype that people who are interested in computers at a very early age are nerds and therefore are worthless,” said a DHS official who asked not to be identified. “We are graduating more performing arts majors than engineers and pushing kids away from the hard sciences. We’ve dumbed down the education in this country.”
Meanwhile, U.S. adversaries are busy preparing for the future cyber battlefield. North Korea has established a recruiting system that identifies child prodigies at an early age and puts them on a path to becoming "cyberwarriors" for the government.
A DEBATE OVER PREPARATION
As the government searches for the next generation of cyber experts, there are differing views over how to train them and where to find them.
Some believe they should be groomed at the growing number of colleges now offering programs focused on cybersecurity. At the University of Maryland, students interested in cybersecurity take a holistic approach, studying not only computer engineering, but also psychology, criminology and public policy.
This allows them to understand both the technical elements of cybersecurity and the personal motivations of hackers, said professor Michel Cukier, associate professor of reliability engineering at the university.
"Cybersecurity has been seen as a purely technical problem for a long time," Cukier said. "But if you're looking for people to come up with security solutions that address the human component as well, these students have a good chance of helping."
Yet some experts say four-year college programs will take too long to meet the current demand for government employees to defend against cyber threats.
"If I went to many of my colleagues that are generals and I said to them, ‘Sir, we’re going to enter the battle tomorrow and we are out-manned one to ten,’ I don’t think his response to me would be ‘Well, great, we’re going to create a four-year college curriculum and we’re going to fill the gap," Lynn Dugle, president of Raytheon’s intelligence information systems business, said at a conference earlier this year.
Dugle said the government is looking for cyber experts in all the wrong places. Raytheon, which has government cybersecurity contracts, recently hired a high school dropout who worked at a pharmaceutical plant and spent his nights displaying his hacker skills online, where he impressed Raytheon recruiters, Dugle said.
'NOT YOUR NORMAL EMPLOYEE'
Such unconventional recruiting methods are crucial to finding the best and brightest from the hacker community, said Johnny Long, a famous hacker. To hire the most talented hackers, the government needs to drop educational requirements and recruit based on hacking skills alone, he said.
The government would be better served by allowing contractors –- who already do a large amount of government cybersecurity work -– to handle recruiting because hackers believe working for contractors is "not as creepy" as working directly for the government, Long said.
That is because hackers often view the government skeptically, primarily because they see federal agencies pushing for laws that put other hackers behind bars, Long said. The government has "cast a dark cloud over the hacker community," he added.
Even so, both the government and contractors have hired numerous hackers over the years. Jonathan Ripshy Duncan, 23, said he once worked in cybersecurity for a government contractor, but would only do so again if given more freedom.
"My job task was the exact same thing every day," Duncan said at DefCon. "If I found something interesting, I couldn't do anything about it. I had to report it and that was it."

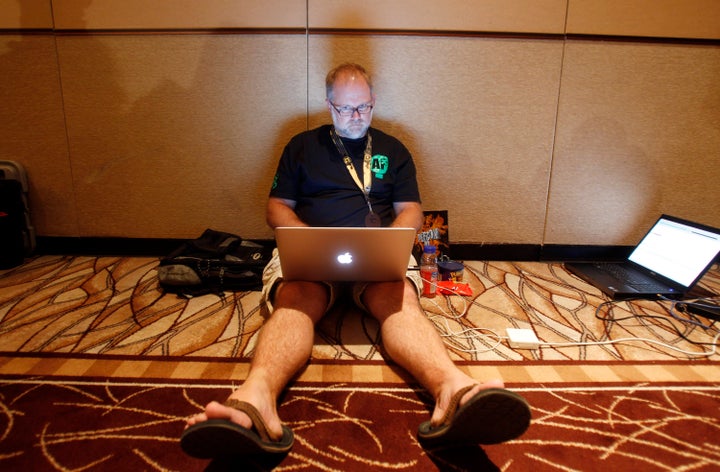
Kevin Broumback (left) and Jonathan Ripshy Duncan said they would like to work for the government, but expressed concern about acquiring security clearances and job restrictions
Duncan's frustration with government work is not uncommon among hackers. The government has done a poor job of managing them by requiring that they adapt to its restrictive environment, Long said.
"Hackers are not your normal employees," he said. "They have different work habits. They sometimes work odd hours. They're skipping lunch. They don’t want to show up in a suit. If you let them operate the way they operate best and don’t put all these restrictions of them, you're going to get a great employee who is loyal."
LONG WAIT FOR CLEARANCES
Even if federal officials can persuade hackers to work for the government, there can be roadblocks to acquiring a security clearance.
Many people with the necessary cyber skills are not U.S. citizens and therefore do not qualify for security clearance, according to experts. And during the financial downturn, many federal employees were denied or lost security clearances due to financial issues, said Evan Lesser, director of ClearanceJobs.com. Filing for foreclosure or bankruptcy, having a spouse lose a job or having a diminished 401k are all viewed as internal security threats.
Those who do qualify for clearances can face long waits. Thirty-five percent of federal employees say it took three to five months to get a security clearance, 31 percent of people said it took between 6 to 11 months, and 13 percent said it took a year or more, according to a recent survey by ClearanceJobs.com.
Because they are handling classified information, government cybersecurity workers often require the highest levels of security clearance, including lengthy background checks and sometimes a polygraph test. Across the federal government, there is a backlog of between 5,000 and 10,000 employees waiting for security clearances, Lesser said.
"A lot of companies who win government contracts need cybersecurity candidates yesterday,” he said. “When you have such an intense need, two months seems like forever.”
Back at the hacker conference, Kevin Broumback, 24, a computer expert from Cincinnati, said he would love to have a job with the federal government because it would mean a steady paycheck with benefits, but he did not think he could acquire a security clearance based on his history.
"I know for a fact I could never gain a top-secret security clearance," said Broumback. "I'm never going to get a job with the government. It's just not going to happen."
The government would prefer to hire young computer experts because they typically don’t have a history of financial woes, messy divorces or foreign travel that can slow down the clearance process, Lesser said.
For this reason and others, federal officials also participated in the first annual DefCon Kids conference, which ran concurrently with the larger hacker conference this weekend in Las Vegas.
In between cracking codes, picking locks and building robots, children sat through a panel discussion with federal agents. Sitting in the front row, Schuyler St. Leger, 11, of Phoenix, who taught himself programming code and built his own home security system, shouted questions to the panelists.
Schuyler said working for the government someday “could be very interesting.”
“You can work with high-level people and do things that can be very important,” he said.
Afterward, Schuyler posed for pictures with the federal agents –- the first contact in what the government hopes will be a future career defending the nation in cyberspace.