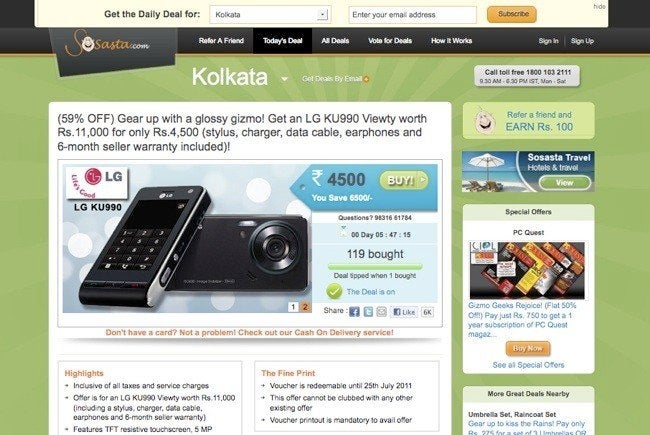
With hackers stealing and publishing private data every other day, the last place you'd expect a data leak to come from is inside a company. But according to a report by Australia's Risky Business, that's what happened on Tuesday at Groupon's India-based website, SoSasta.
Security consultant Daniel Grzelak claims he was searching Google on June 24 when he discovered the massive database, which includes the email addresses and passwords of thousands of SoSasta users.
"I started scrolling, and scrolling and I couldn't get to the bottom of the file. Then I realised how big it actually was," Grzelak told Risky Business's Patrick Gray, who estimates that 300,000 user accounts were compromised.
ZDNET's India IT blog reports that Groupon sent the following email to local users on Monday:
Over this weekend, we've been alerted to a security issue potentially affecting subscribers of Sosasta. We wanted to let you know that the issue has been brought under control and your accounts are secure. However, as a precautionary measure, we recommend that you change your SoSasta password immediately, by visiting the SoSasta website[...]
Please be aware that none of your financial information (Credit Card, Debit Card, NetBanking etc) has been compromised since this information is not stored on SoSasta, as per law.
However, writes ZDNET, the email apparently did not reach all Sosasta's users.
Groupon's U.S. customers shouldn't be affected by this leak, according to a statement Groupon sent to Risky Business. "Sosasta runs on its own platform and servers, and is not connected to Groupon sites in other countries," said the statement.
Grzelak noted to Risky Business that these accidental leaks occur fairly often, though not usually as large. He told risky business that he was searching Google on Friday for "publicly accessible databases containing e-mail address and password pairs," such as those that have been exposed in recent LulzSec hack attacks, among other security breaches. Grzelak has compiled a list of such information at ShouldIChangeMyPassword.com, where users can check to see if their personal information has been made public.
