Since I started helping people with online reputation issues, I have heard some amazing tales but few as educational as this one. A lady called me up with an awful problem. Her phone had been stolen from her locker at her job and now, yes you may have already guessed it, inappropriate pictures of her were now on the Internet. She made three mistakes, all preventable. Yet, the main lesson is that we all need to make our mobile phones valueless.
First, what the girl did wrong. Taking naked pictures of oneself -- duh! This one confounds me but just continues-on in our society. We need to teach our sons and daughters not to do this, and also teach them not to ask it of other people. In addition, this young lady failed herself in two other technical categories. She didn't enable the passcode feature on her phone, and she didn't set up the Find My iPhone/remote data-erasing features. In her case, three strikes equaled revenge porn.
Sadly, we can buy purchase protection to replace a lost or stolen phone, but no such insurance exists for a damaged reputation.
On to my main point, if you truly want to protect yourself from the many perils of a lost or stolen phone, you need to have everything of value backed up, preferably automatically. If you lose possession of your phone, the physical value of your phone should be the only concern you have. Here's how you do it, and the cloud service providers are going to love me.
Email. Many of us transact most of our business through e-mail, and we would be lost if a month's worth or even a few day's worth of e-mails were permanently lost. Prevent this by using an e-mail platform that saves all of your e-mails in the cloud such as a virtual exchange server or even G-mail which enables you to check e-mail from multiple devices. When using this type of service, if you change your password and/or wipe your phone, then no one can access your e-mail except you.
Pictures and music. Photos document life's moments and you certainly don't want to lose your memories if your phone ends up in the ocean (or a pitcher of margaritas, but that's another story.) The same is true for your music. Set up your phone to automatically back it up to the cloud, so you have copies without even thinking about it.
Notes and other stuff. If you take a lot of notes on your phone, make sure they are backed up or use one of the cloud-based note services like Evernote. If your phone disappears, then all you need to do is change your password and your notes are safe.
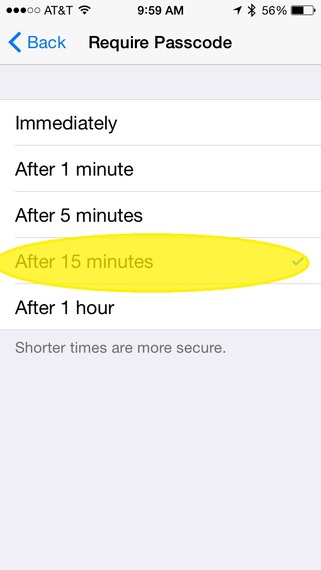
Set up the passcode on your phone. I will admit that I didn't use this feature initially on my iPhone but now it is a necessity. It requires you to enter a 4-digit code to access your phone. You can set it so that it is required each time you open it or after your phone has been idled for a set amount of time, up to one hour. There are 10,000 possible codes so it is not easily hacked, unless you choose the lazy path and use 1234, 0000 or your birth year. Five years ago, Informationweek published a piece on this which is still relevant. Use a passcode and try to make it unique.
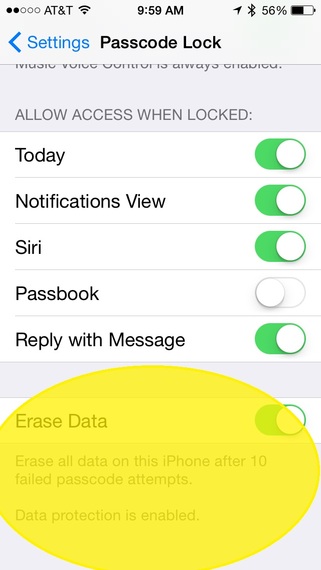
Be prepared to wipe. This is the heart of the "make it valueless" proposition. Essentially, you should be prepared to wipe your phone of all its information at any time. All of your data and anything important should be backed up to the cloud so that if your phone is lost or stolen, your information won't be compromised. Both Apple and Android phones offer this, but you have to set it up. In addition, I recommend that you enable the setting on your iPhone to automatically wipe it if the passcode is entered incorrectly after 10 attempts.
Yes, I know that you may forget your code or one of your friends may mess with you and accidentally wipe your phone, but more than likely this feature could help you more than it could harm you. It's much easier to deal with a lost phone than lost personal data.
Google recently announced plans to de-list revenge porn sites, which is a great step toward a more-civilized society, but believe me, no one wants to deal with compromised or lost data, particularly when it is easily preventable.
This post originally appeared on DavidPR.com.