This post was co-authored by D.S. Kane, author and former economist, intelligence service operative and university faculty member.
It's called the Web for a reason, and as it is with most webs, eventually some living thing gets caught in the middle. Interestingly, the same goes with a net.
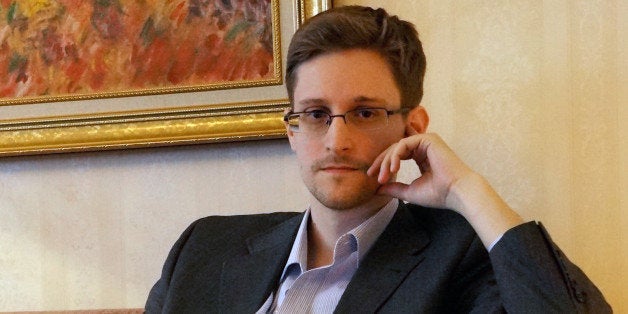
This past year, the one at the center of a Web-based conflict over privacy rights and constitutional freedoms is former U.S. National Security Agency contractor, and classified document leaker, Edward Snowden.
Since last June, when The Guardian and The Washington Post reported that the NSA was illegally spying on millions of U.S. citizens and collecting private data from Google and Facebook, using a secret surveillance program called PRISM, there was only one thing Snowden could do -- decide where to hide. But in the past few weeks, he's come out of hiding and faced the public, so-to-speak, first via Google Hangout at SXSW and this week he spoke at the TED Conference in Vancouver via robot from somewhere in Russia.
Many have called him a traitor. Others claim he's a hero. Regardless, his arguments are focused less on his own image, safety and security, than they are at pointing global attention toward the expectation to privacy of American and international citizens.
"[The NSA] said, we don't track [American communication] stats, and we can't track those stats. We can't tell you how many communications we're intercepting around the world, because to tell you that would be to invade your privacy," said Snowden, at TED Vancouver. "[But] what Boundless Informant tells us is more communications are being intercepted in America about Americans than there are in Russia about Russians."
In his latest appearances, Snowden has also advocated for the upholding of the U.S. Constitution and the necessity for greater cybersecurity.
"[While] working in the intelligence community, I saw a lot of things that disturbed me," said Snowden. "We do a lot of good things... but there are also things that go too far, that shouldn't be done, decisions that were being made in secret... without our consent, and without even our representatives in government knowing they were being done."
In Austin, a few weeks ago, he claimed that the, "Constitution was being violated on a massive scale," and that the rights of the people, per the Fourth Amendment, were being infringed upon.
Snowden's clear and present message is that "All [Internet] companies need to move to an encrypted browsing habit by default. That'll increase the privacy and the rights that people enjoy worldwide."
In 1997, Louis Freeh, then FBI Director, said, "The widespread use of robust non-key recovery encryption ultimately will devastate our ability to fight crime and prevent terrorism." Now, nearly 17 years later, the NSA has access to every cell phone conversation and every email and text message any American sends or receives, as well as private communications of people in other nations.
In addition, Snowden points out, unencrypted information on the Web is not only seen by the NSA, but also, "the Russian intelligence service can see a record of that, the Chinese service can see a record of that, the French service, the German service, the services of Andorra. They can all see it."
So what does NSA Deputy Director, Richard Ledgett, have to say about all of this? When Ledgett spoke at the TED Vancouver Conference on Thursday -- just two days after Snowden's virtual appearance -- he admitted, "There are some kernels of truth in there, but a lot of extrapolations and half-truths." He also agreed that the NSA needs to be "more transparent, but not in a way that allows the bad guys to counter." His argument against Snowden's "one-sided" point of view is that the American people should, "Learn the facts. Look at the data."
Those in favor of Snowden's decisions would contend that without the information revealed in the leaked documents, we would not have known any of the facts. As a result of his actions, and those of other whistleblowers, we're no longer ignorant to the plethora of data tracking systems used by the United States, some of which are used against its own citizens.
Who ever heard of PRISM before? Who knew intelligence agencies -- principally the NSA -- operated so many different identity tracking systems and disinformation systems? Of the nearly 40 systems out there, which read like an alphabet of suspicion, those we're now familiar with include ACQUAINT, Boundless Informant, Bullrun, ECHELON, FAST, GUARDIAN, Mystic, NGI, PRISM, PROMIS and TIP. It can make a person wonder just how far back this invasion of our right to privacy goes.
The real problem with Snowden's actions, asserted Ledgett, has more to do with the interference of our national security, than anything else.
"The actions that he took were inappropriate because of the fact that he put people's lives at risk in the long run," said Ledgett. "The capabilities [of the NSA] are applied and very discreet and measured in controlled ways, so the unconstrained disclosure of those capabilities means that as adversaries see them, and recognize, 'Hey, I might be vulnerable to this,' they move away from that... The net effect is that our people, who are overseas... are at greater risk because we don't see the threats that are coming their way."
When President Obama signed the "National Defense Authorization Act" (NDAA), H.R. 1540 into law on December 31, 2011, the new law codified indefinite military detention without charge or trial into law for the first time in American history.
Obama justified the NDAA as a means to combating terrorism, as part of a "counter-terrorism" agenda. But in substance, under the provisions of the NDAA, any American opposed to the policies of the U.S. government can be labeled a "suspected terrorist" and arrested under military detention, indefinitely.
At TED Vancouver, Snowden explained, "Terrorism has always been what we in the intelligence world would call a cover for action. Terrorism is something that provokes an emotional response that allows people to rationalize authorizing powers and programs that they wouldn't give otherwise." As we know, some government officials have already compared Snowden to terrorists for hacking into government computers.
So, what about recent news that the CIA hacked into the computers of the U.S. Senate? Is the CIA subject to the laws of the United States? If CIA operatives did hack the Senate's computers, is that an act of terrorism?
There have also been reports that the U.S. Senate may have hacked into the CIA's computers. Is the Senate subject to the same U.S. laws? By that standard, has the Senate committed an act of terrorism?
If Snowden broke the law, wouldn't the same be so of U.S. intelligence agencies?
Should we punish whistleblowers when their best efforts are directed toward ensuring that our own government acts within the Constitution?
Must we sacrifice liberty for safety?
These questions lie at the heart of the argument at the center of the web.
On November 11, 1755, Benjamin Franklin stood for the Pennsylvania Assembly in its Reply to the Governor and said, "They who would give up essential liberty, to purchase a little temporary safety, deserve neither liberty nor safety."
--
D.S. Kane is an author and former economist, intelligence service operative and university faculty member. The first novel in his techno-thriller series, "Bloodridge," is set for release in summer 2014. He has also written articles on computer fraud and countermeasures, banking, economics and other finance topics. Sharing only some of his intelligence service knowledge with others, he has spoken at numerous writers events, including the Pikes Peak Writers Conference on "True Lies: Writing Covert Training and Missions into Fiction," and twice served as the keynote speaker at the Maui Writers Conference. He also teaches fiction writing.
