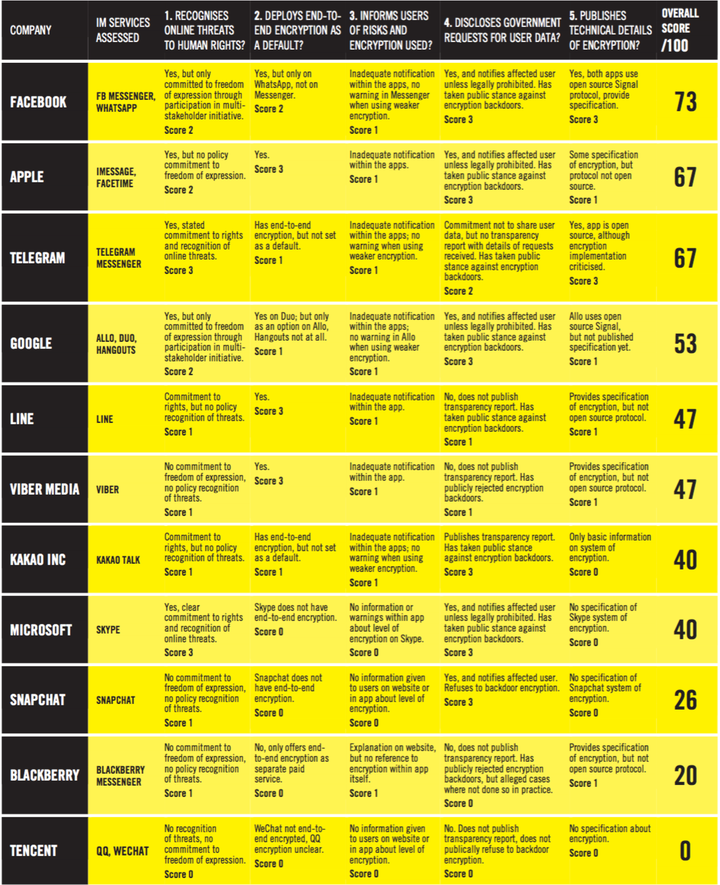
More than half of the the world’s internet users are on IM every day and for many people some of their most private conversations and information is shared on these services. In a report published by Amnesty International last week, only three tech companies were named as having fully enabled end-to-end encryption: Apple, Line, and Viber Media. Snapchat placed second-to-last on the list with “no commitment to freedom of expression” and “no policy recognition of threats.” The app doesn’t have end-to-end encryption and does not provide information to users on the level of encryption they should expect when using the service. Skype ranks similarly to Snapchat with no end-to-end encryption. The highest ranking services are Facebook’s WhatsApp (not Messenger), and Apple iMessage/Facetime which provide stronger data-protection and transparency with user notifications and encryption specification.
All of the companies in the report provide basic transport encryption. This flavor encrypts messages while they are in transit but gives companies access to the content of messages. The incentive to only supply transport encryption is largely due to advertisers and gaining insight into user’s habits and desires. The idea is to build a profile similar to web-based advertising. Companies that are adding intelligence-powered services to apps will also take advantage of unencrypted content.
A lot of users might think that having only transit security is fine, but an issue arises when service providers’ own systems are compromised. This leaves a user’s personal content at risk. Successful attacks like this have already been made against Google, Yahoo, and others. Furthermore, users are forced to trust the individuals who work on the product to not search through their personal information. For instance the AP recently wrote about U.S. police officers’ widespread abuse of confidential databases “to get information on romantic partners, business associates, neighbors, journalists and others for reasons that have nothing to do with daily police work.” The same type of database exists when unencrypted messages are being stored, whether temporarily or permanently, on IM systems.
One proposal is to have end-to-end encryption and create a backdoor or secret key so states can access user data when needed. This is also dangerous considering anyone ― criminals, malicious attackers, governments ― can find the key or backdoor and begin to exploit it to access private information. Microsoft recently had their golden key released, allowing operating system checks to be bypassed. A master key is a single point of failure. All of the companies in the report said they wouldn’t allow a backdoor except Tencent (QQ, WeChat) who received a score of 0. There is consensus among security experts that maintaining a safe backdoor is impossible.
End-to-end encryption is the only solution that the cryptographic community supports. Some companies listed in the report allow the use of end-to-end but they don’t set it as a default due to the business and advertising reasons above. The only way to compromise this form of encryption is to gain access to one of devices of the parties in communication. Otherwise end-to-end is secure against attackers, governments, and to employees of the company that run the messaging service.
Another issue raised in the report is whether companies who provide end-to-end encryption turn it on by default. There’s a monetary incentive for them to leave it up to the user (off by default), which leaves users exposed when they might think that because an app provides this encryption that it is automatically enabled. Google’s Allo, Telegram, and Kakao have such default settings.
Providing end-to-end encryption is already a solved problem. WhatsApp uses an open-source protocol named Signal that anyone can implement. It’s freely available. The cryptographic community has labeled this the “gold standard” in securely communicating on IM services. Companies choosing not to implement Signal are putting innocent users at risk and they’re doing so for profit and nothing else. Facebook Messenger is an example of a service that doesn’t use Signal even though their other messaging product WhatsApp does.
Discussion around data-security is becoming increasingly public with cases like Apple v FBI in which the FBI tried to gain access to the phone of one of the San Bernandino terrorists. They wanted Apple to build a backdoor to the device, however that would have created the ability to backdoor any device. Tim Cook claimed this was a “breach of privacy.” There is a balance that needs to be struck. The Amnesty International report appropriately claims that “surveillance of private communications always entails an interference with human rights, but it can be justifiable if it meets strict requirements under international law. Surveillance is only justifiable when it occurs based on reasonable suspicion, in accordance with the law, is strictly necessary to meet a legitimate aim (such as protecting national security or combatting serious crime) and is conducted in a manner that is proportionate to that aim and non-discriminatory.”
It’s important to also note that governments abuse unencrypted data for political reasons. One instance is Ethiopia where the government is recording phone calls with family and friends and using them in arbitrary interrogations. Another is GCHQ, the British intelligence organization, developing a program to target people who haven’t been charged with any crime in hopes of manipulating them or ruining their reputation.

