Sony has finally begun to restore access to the PlayStation Network, after a massive security breach that exposed of the personal information of over 100 million users. But the true extent of the breach -- and the state of Sony's security -- are still largely unclear.
Sony has faced scrutiny from Congress and backlash from angry consumers, some of whom have already changed gaming systems as a result of the data breach. Though the PlayStation Network is back online, considerable uncertainty remains as to just how much personal information was exposed. Experts also say that the network itself may not yet be totally secure.
According to a Reuters report, Sony's security weaknesses could be more widespread than the company has acknowledged. John Bumgarner, a security researcher, discovered a number of remaining flaws in the system that he has said could easily be exploited. Notably, Bumgarner showed that a simple Google search could be used to discover pages of information which could be used to launch more advanced attacks, including the names, email addresses and phone numbers of Sony's IT managers.
"Sony still has several external security issues that need to be addressed," Bumgarner told Reuters.
Since the breach, Sony has promised to step up security, saying in a press release that it has made "considerable enhancements to the data security" by adding advanced technologies, increasing software monitoring, conducting vulnerability testing, increasing encryption and implementing additional firewalls. In addition, the company says it has added an early-warning system for unusual patterns to help detect breaches earlier.
Previously, Sony had been protecting passwords using "a cryptographic hash function," which is vulnerable to attack through basic means.
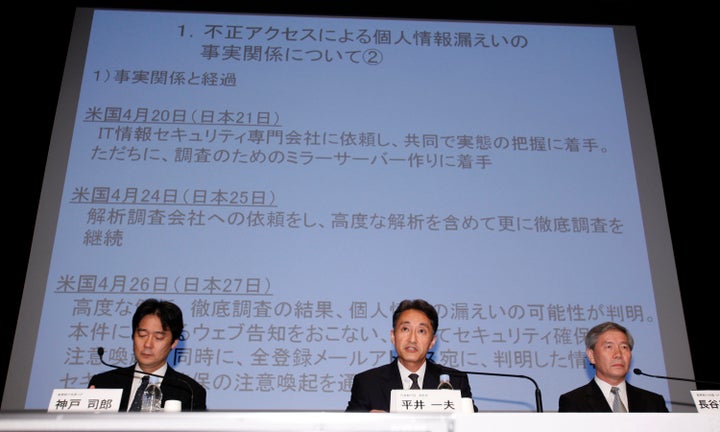
Sony first confirmed the attack -- which it has blamed on the online collective Anonymous, though Anonymous has denied any responsibility -- on April 26, despite the fact that it was believed to have occurred between April 17 and April 19. Sony has been criticized for its delay in notifying both law enforcement and consumers following the breach.
Sony has begun to restore access in the Americas, Europe and several other countries, though the company is holding off in Japan and other Asian countries. According to the Wall Street Journal, Sony is "still in talks with Japan's industry ministry, which is asking for more detailed explanation on how Sony's online service works and what security measures the company is implementing."
When it comes to the nature and extent of the breach itself, experts say that little is known. Of the many rumors that have floated around, the one that hackers may have taken credit card numbers and sold them online is especially concerning. Yet some believe that it may have been the biggest data breach in American history.
"This is arguably the most serious breach in U.S. history measured by number of people involved, sensitivity of information accessed, and amount of time that the breached network has been shut down," said Fred Cate, Director of the Center for Applied Cybersecurity Research at Indiana University. "Even now, only parts of the PlayStation network are being brought back into service."
Though the company initially announced that the network would be restored in days, those days became weeks. Sony now says American services should be restored by the end of May.
"While we understand the importance of getting our services back online, we did not rush to do so at the expense of extensively and aggressively testing our enhanced security measures. Our consumers' safety remains our number one priority," Sony executive deputy president Kazuo Hirai told customers in a video.
For users who use the same password across sites, the Sony breach endangered not only PlayStation Network accounts, but any other account using the same username and password combination. Experts underscored the importance of assigning unique passwords to each account.
"For consumers, the key lesson is to use unique passwords," said Cate. "It is boring and tedious and no one wants to do it, but it is the only way to guard against the risks presented by the PlayStation breach."