
One of the greatest national security threats the United States faces today is the one we are least prepared for: cyberwarfare. As demonstrated by the “WannaCry” cyberattack launched on May 12, 2017, no system is invulnerable to cyberattacks. While the United States government has responded to these attacks via executive order in an attempt to improve federal cybersecurity, there is more the government can do to bolster protect governmental system framework from cyberattacks, particularly with regard to safeguarding critical systems such as those of the Department of Homeland Security (DHS).
Cybersecurity attacks are an increasing threat to federal government systems. While the May WannaCry attacks are just one instance of the rising danger of cybersecurity threats, this attack serves as a prime example of the necessity to update federal computer networks and systems.
Launched on May 12, 2017, the “WannaCry” cyberattack was a ransomware attack that affected hundreds of thousands of systems worldwide (See Figure 1). At a House hearing before the Committee on Science, Space, and Technology in July of 2017, cybersecurity experts from Kryptos Logic announced that the WannaCry attack, as it is now referred to, affected the systems of over 120 countries, each with one thousand or more hacking attempts, and over 190 countries with five to ten ransom attempts.
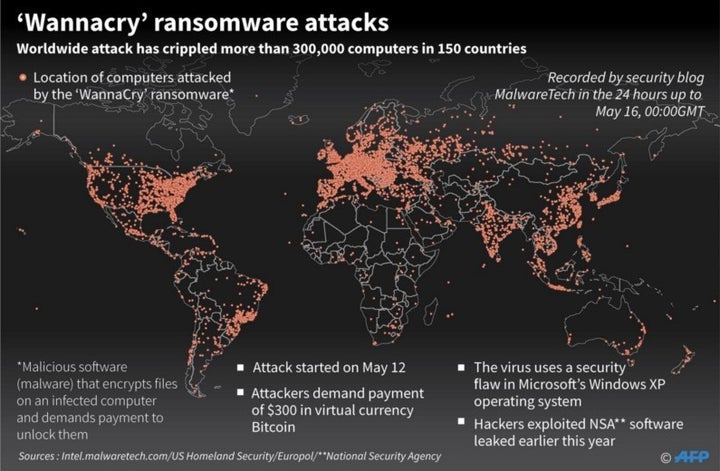
With regard to the specific components of the WannaCry attack, the worm was designed to encrypt files on a computer or system and only allow the individual to decrypt their files after paying the hacker 300 bitcoins, a form of currency increasingly used and increasing in value. However, on the date of the attack, employees from Kryptos Logic discovered a “kill switch” that allowed them to disable the ransom portion of the cyberattack. It is estimated that if the kill switch had not been discovered, nearly 65 million more systems would have fallen victim to this cyberattack, the most vulnerable states being China, Russia, India, and the United States according to cybersecurity experts testifying before the House Committee on Science, Space, and Technology.
Though the federal government’s system were not affected nor compromised by this cyberattack, they do establish the rising threat future cyberattacks could pose both to national security and computer systems throughout America.
In reaction to this cyberattack, among other denial of service (DOS) attacks, President Donald Trump issued Executive Order (EO) 13800, an executive order designed to mandate all federal agencies under the executive branch implement a NIST framework (see Figure 2), a highly acclaimed framework which would greatly improve the cybersecurity of federal systems. Furthermore, under this executive order, each agency or department would be required to annually report to the DHS and the Office of Management and Budget with regard to system safety.
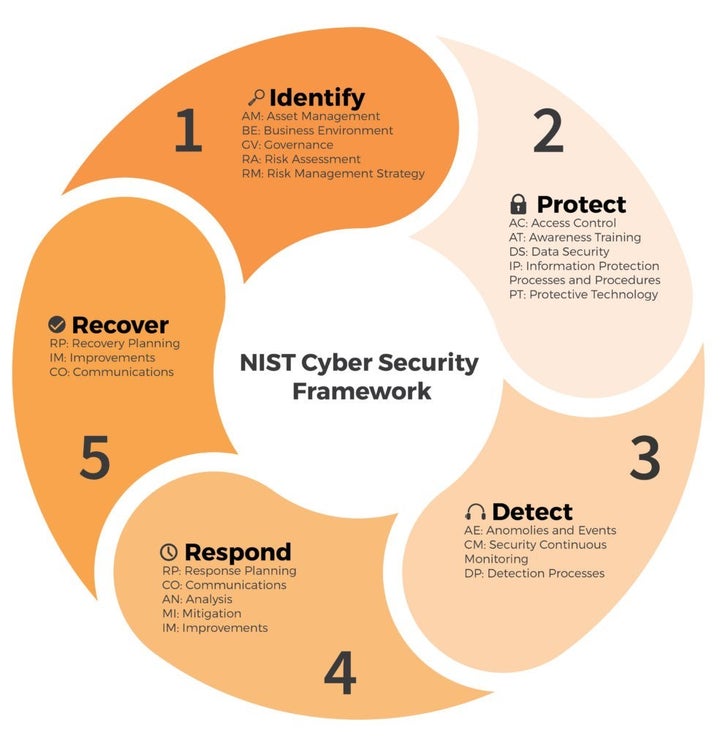
Figure 2: NIST Cyber Security Framework Protocols
While steps to bolster federal cybersecurity have been taken via EO 13800, more action is needed to ensure that federal systems are better safeguarded against attack. One step is through the passage of H.R. 2774, titled the “Hack DHS Act”. Introduced by Representative Ted Lieu [D-CA-33] on June 6, 2017, this bill proposes the establishment of a “bug bounty program”, defined as a “program under which an approved computer security specialist or security research is temporarily authorized to identify and report vulnerabilities within the information system of the” DHS in exchange for monetary payment.
Following the completion of relevant background checks on third party computer security specialists, the DHS bug bounty program will assign relevant systems and operations to be analyzed by security specialists in search for vulnerabilities. This will then be followed by the proposal of remedies for those vulnerabilities.
Furthermore, given that this bill’s proposed program greatly mirrors a previous initiative by the Department of Defense (DOD) titled “Hack the Pentagon” which held the same express purpose and structure, DHS will receive recommendations from the DOD. This bill also requires a written report be submitted to the committee on Homeland Security of the Senate and House of Representatives by the Secretary of the DHS no later than 90 days following the program’s establishment. The report will document the security researchers involved in the program, their findings, and their solutions. The bill additionally authorizes that $250,000 are appropriated for fiscal year 2018 to pursue this endeavor.
It is important to note, however, that several arguments can be made both in support and opposition of this bill. The benefits of H.R. 2774 include the fact that this program mirrors a similar and highly successful program launched by the DOD entitled “Hack the Pentagon” which, like this bill’s program, was designed to expose vulnerabilities in DOD’s cyber infrastructure systems. Furthermore, the mission of this program, investigating vulnerabilities in the DHS’s computer systems, is extremely important.
However, some may argue that while this bill does allow for standard DHS protocol to conduct background checks on third-party computer security specialists, the mandate for the establishment of this program prior to 180 days may lead to insufficiencies in the background checks completed, given estimated processing typically exceeds that time frame. Nevertheless, DHS can prioritize the clearance of participants, thereby ensuring proper screening in a timely fashion. Additionally, some may question the necessity of hiring third-party specialists to conduct an infrastructure security investigation given the expertise of current DHS employees. However, a third-party opinion and analysis may discover weaknesses previously overlooked by DHS employees, thus strengthening DHS cybersecurity through further evaluation.
National security is a bipartisan issue of the utmost importance. Given the mounting frequency and sophistication of cyberattacks, the updating of federal systems is critical to strengthening our national cybersecurity efforts. While President Trump’s Executive Order 13800 takes steps towards improving safeguards, passing H.R. 2774 would work to find vulnerabilities in the DHS, a step necessary in order to ensure that DHS systems are better safeguarded against cyberattacks.
